[OCI] OKE Cluster 구축(2) - Network 구성
[OCI] OKE Cluster 구축(2) - Network 구성
해당 가이드는 아래 요건으로 구성되는 OKE Cluster 구축 가이드이며, 이외 다양한 시나리오가 가능합니다.
- CNI Plugin : VCN-Native Pod Networking
- Subnet
- Kubernetes API Endpoint : Private
- Worker Nodes : Private
- Pods : Private
- Load Balancers : Public
- Bastion : Public
1. 개요
1.1. 총 5개의 Subnet 구성
- API Endpoint용 Subnet
- Worker Nodes용 Sunbet
- Pods용 Subnet
- LB용 Subnet
- Bastion용 Subnet
1.2. 각 Subnet CIDR 대역
- API Endpoint용 Subnet : 10.250.0.0/29
- Worker Nodes용 Sunbet : 10.250.1.0/24
- Pods용 Subnet : 10.250.32.0/19
- LB용 Subnet : 10.250.2.0/24
- Bastion용 Subnet : 10.250.3.0/24
2. 네트워크 구성
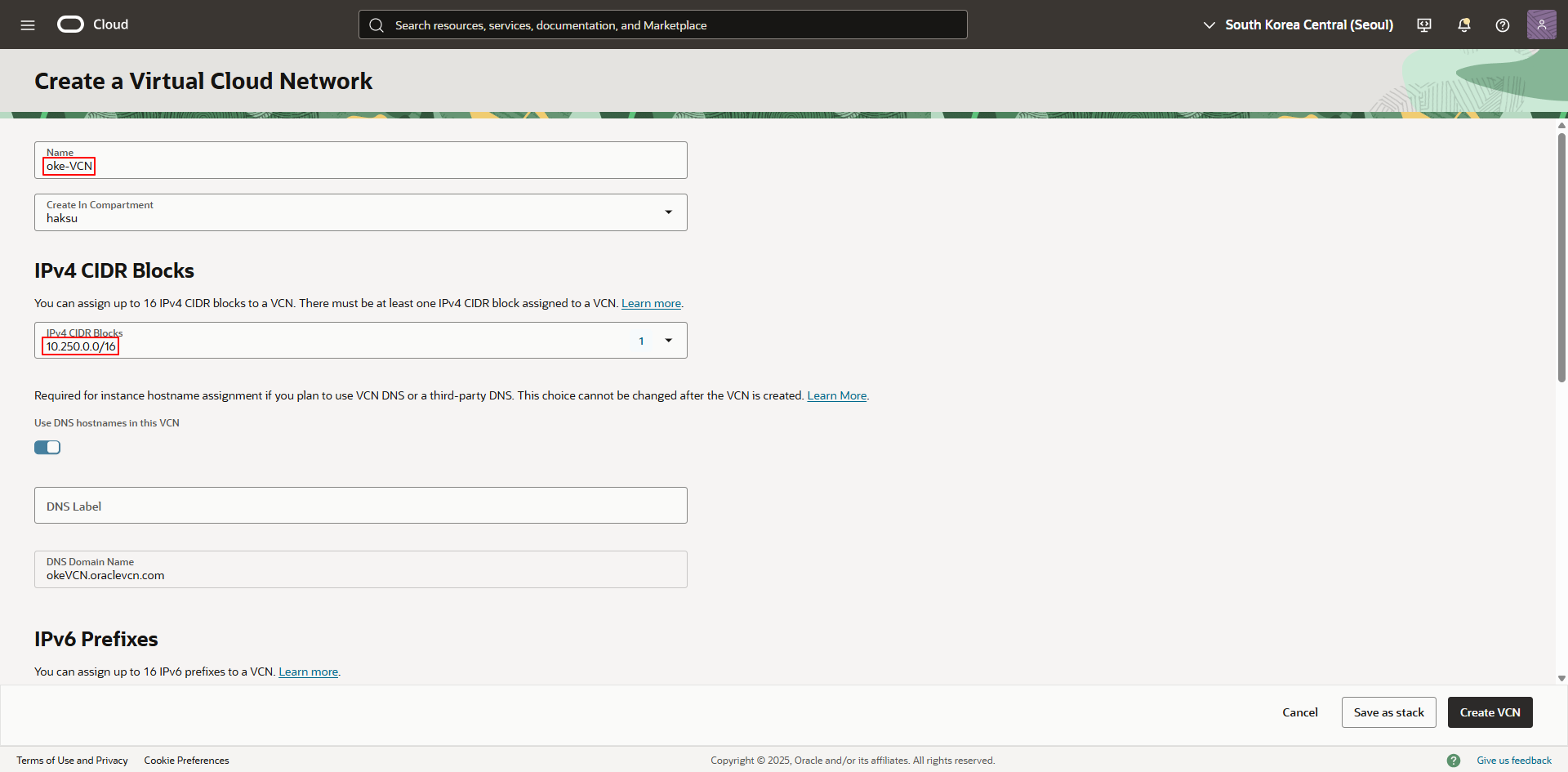
2.1. VCN 생성
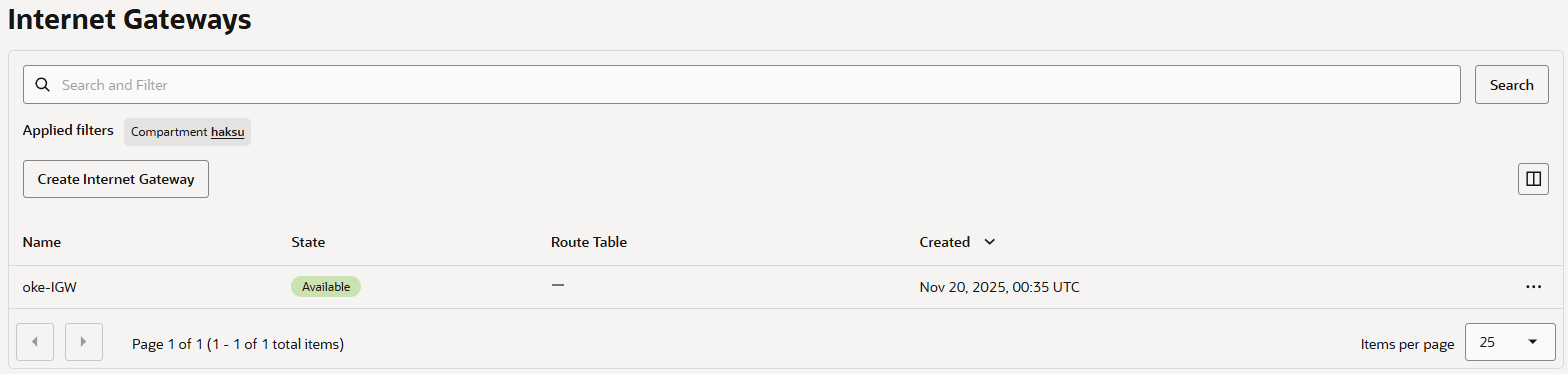
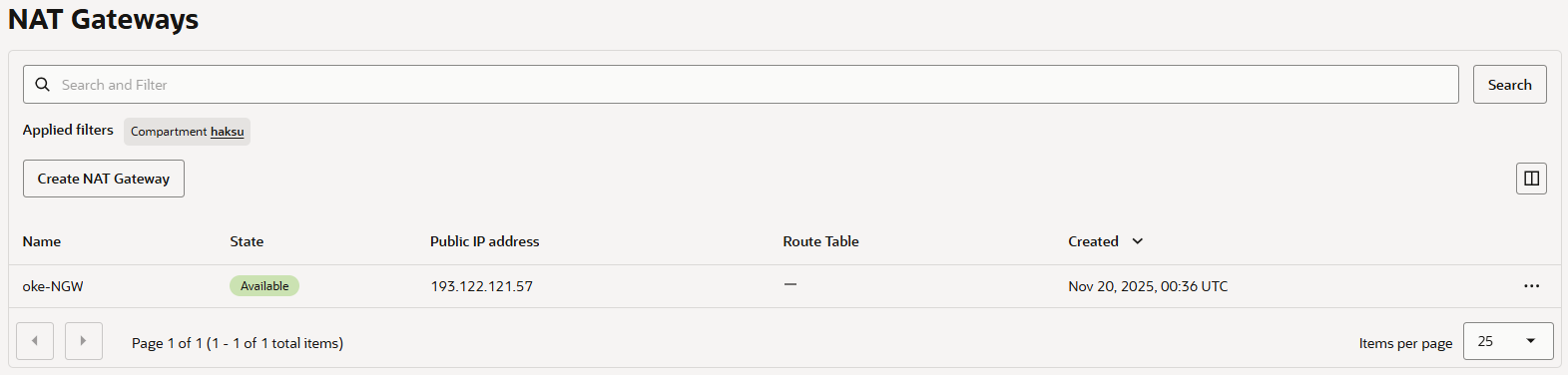
2.2. Gateway 생성
NAT Gateway는 Public IP가 할당되며, Reserved IP를 통해 예약된 Public IP를 할당하는 것이 바람직한 구성입니다.
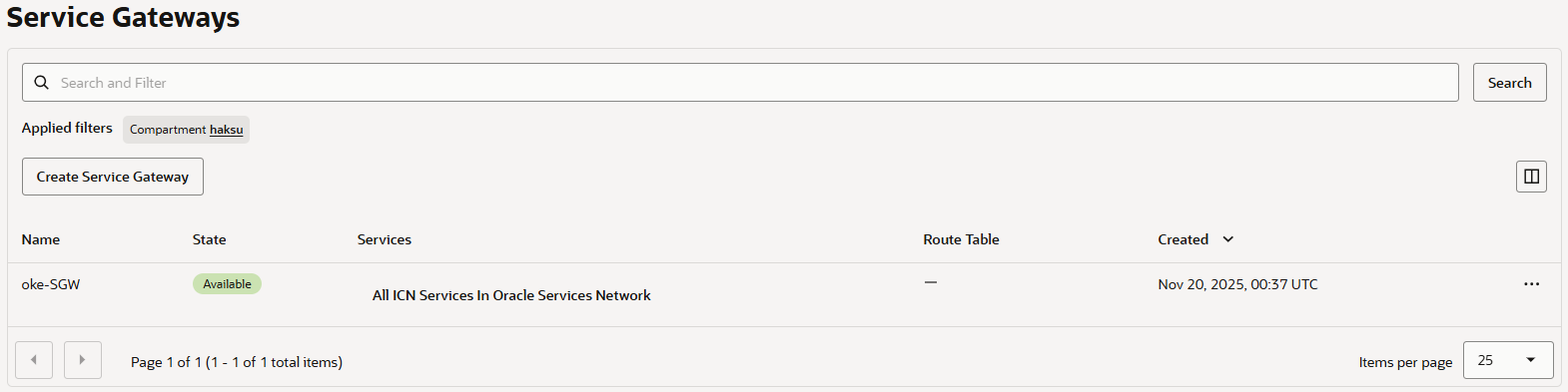
Service Gateway : <적절한 이름으로 생성> / All ICN Services in Oracle Service Network 선택
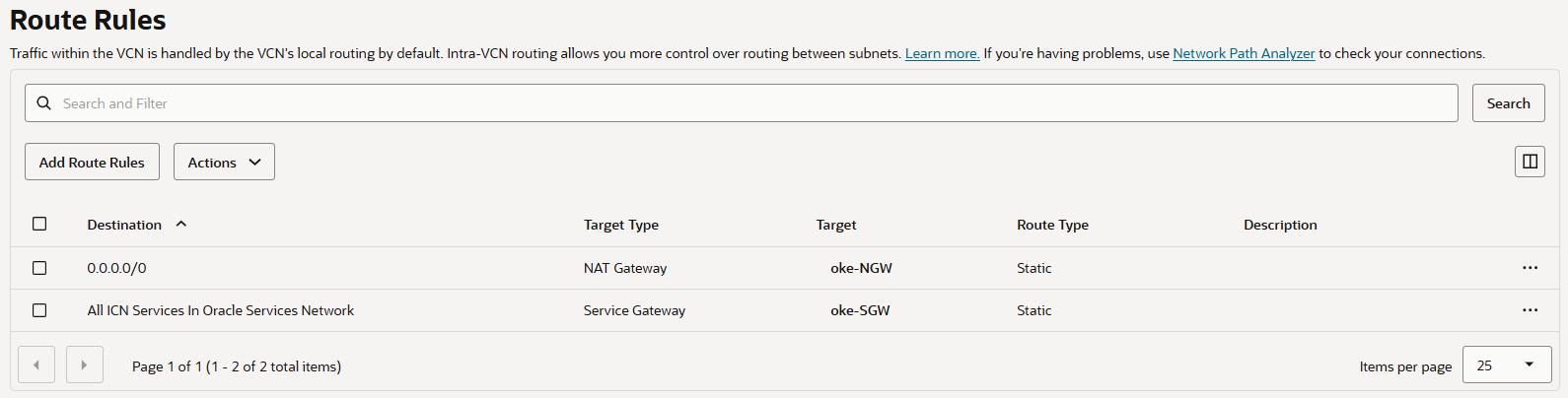
2.3. Route table
2.3.1. API Endpoint Subnet용 Route table 생성
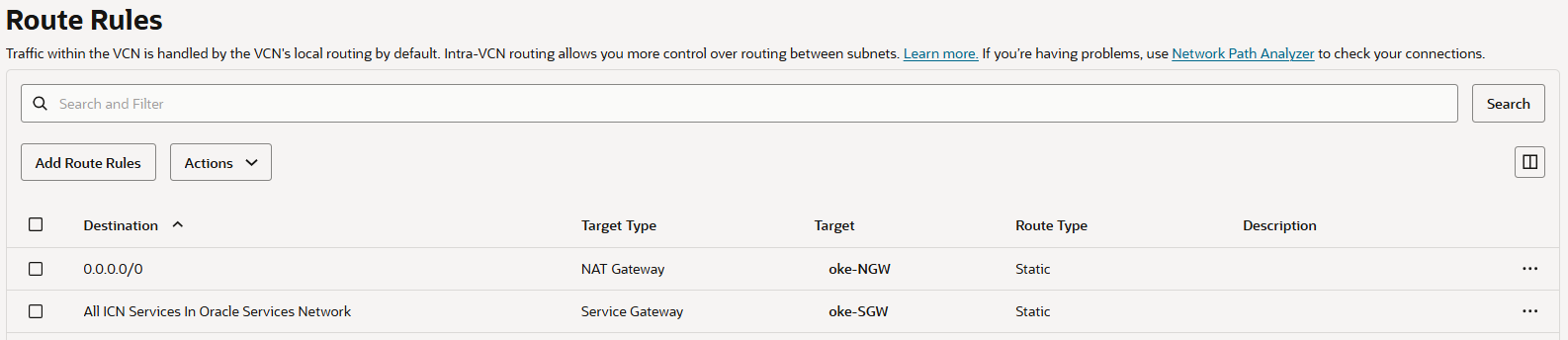
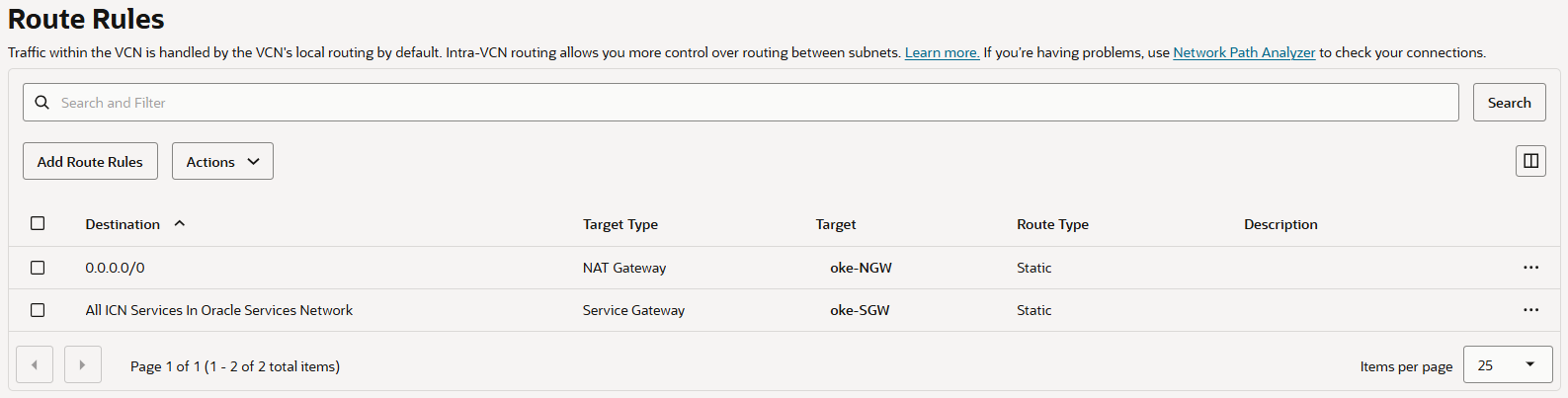
2.3.2. WorkerNode용 Route table 생성
2.3.3. Pod Subne용 Route table 생성
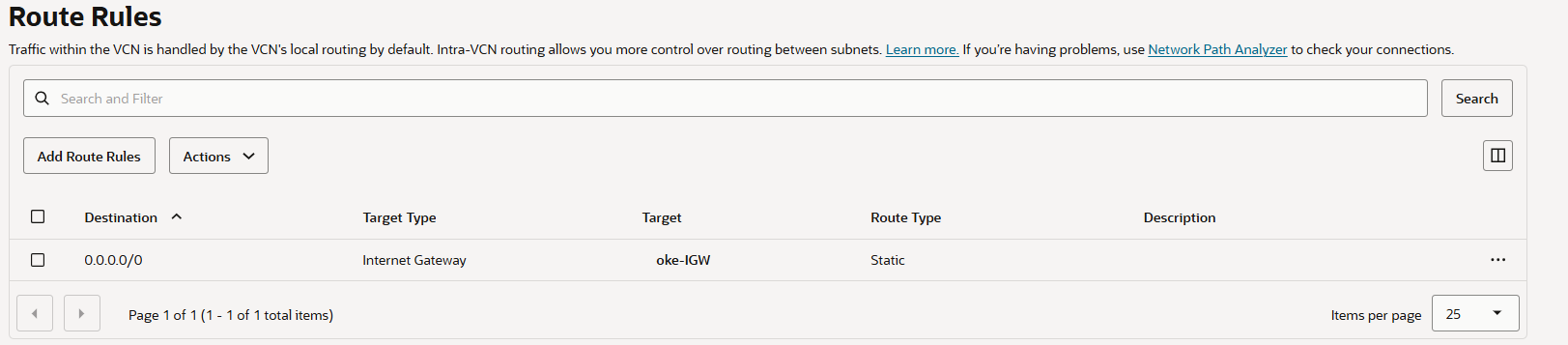
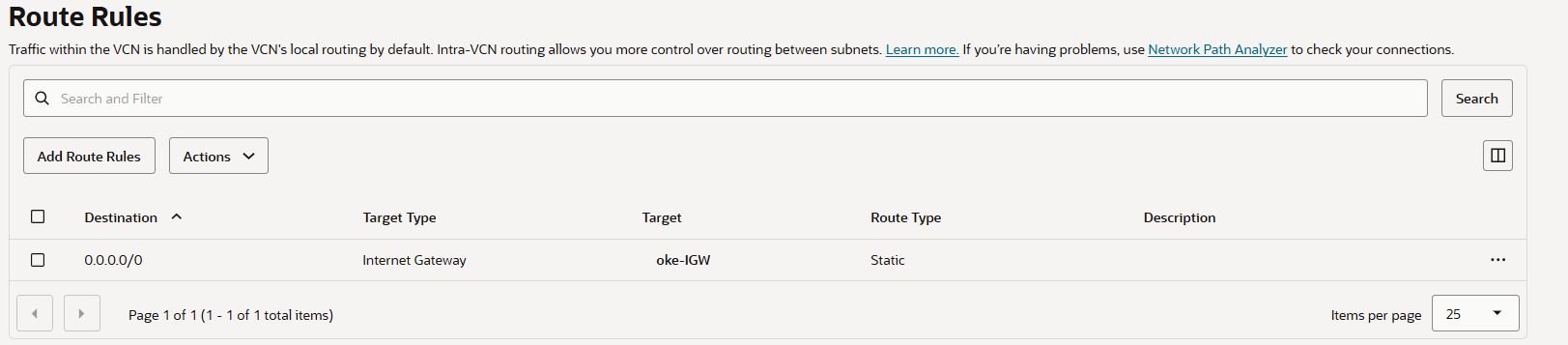
2.3.4. LB Subnet용 Route table 생성
2.3.5. Bastion Subnet용 Route table 생성
2.4. Security List
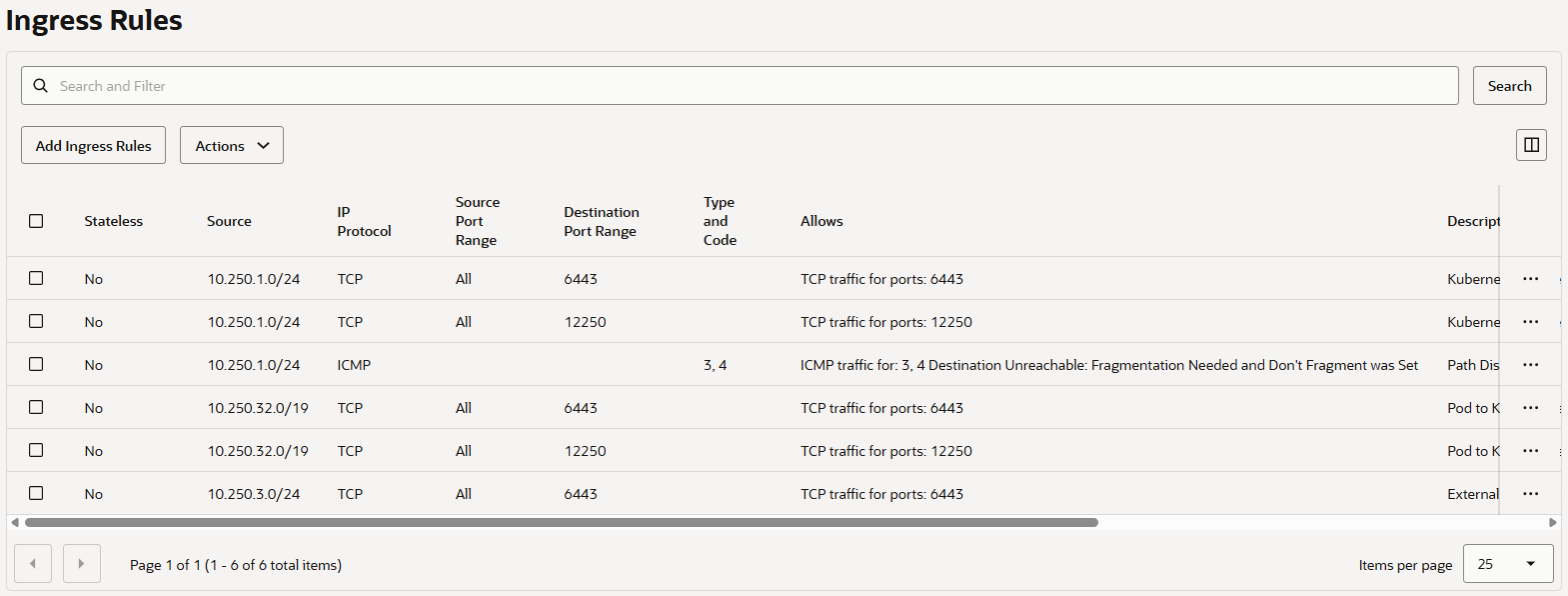
2.4.1. API Endpoint Subnet용 Security List 생성
Ingress
State Source Protocol/Dest. Port Description Stateful 10.250.1.0/24 TCP/6443 Kubernetes worker to Kubernetes API endpoint communication Stateful 10.250.1.0/24 TCP/12250 Kubernetes worker to Kubernetes API endpoint communication Stateful 10.250.1.0/24 ICMP 3,4 Path Discovery Stateful 10.250.32.0/19 TCP/6443 Pod to Kubernetes API endpoint communication (when using VCN-native pod networking) Stateful 10.250.32.0/19 TCP/12250 Pod to Kubernetes API endpoint communication (when using VCN-native pod networking) Stateful 10.250.3.0/24 TCP/6443 External access to Kubernetes API endpoint (Bastion Subnet CIDR when access is made through OCI Bastion) Egress
State Destination Protocol/Dest. Port Description Stateful All ICN Services In Oracle Services Network TCP/ALL Allow Kubernetes API endpoint to communication with OKE Stateful All ICN Services In Oracle Services Network ICMP 3,4 Path Discovery Stateful 10.250.1.0/24 TCP/10250 Allow Kubernetes API endpoint to communicate with worker nodes Stateful 10.250.32.0/19 ICMP 3,4 Path Discovery Stateful 10.250.32.0/19 ALL/ALL Allow Kubernetes API endpoint to communicate with pods (when using VCN-native pod networking)
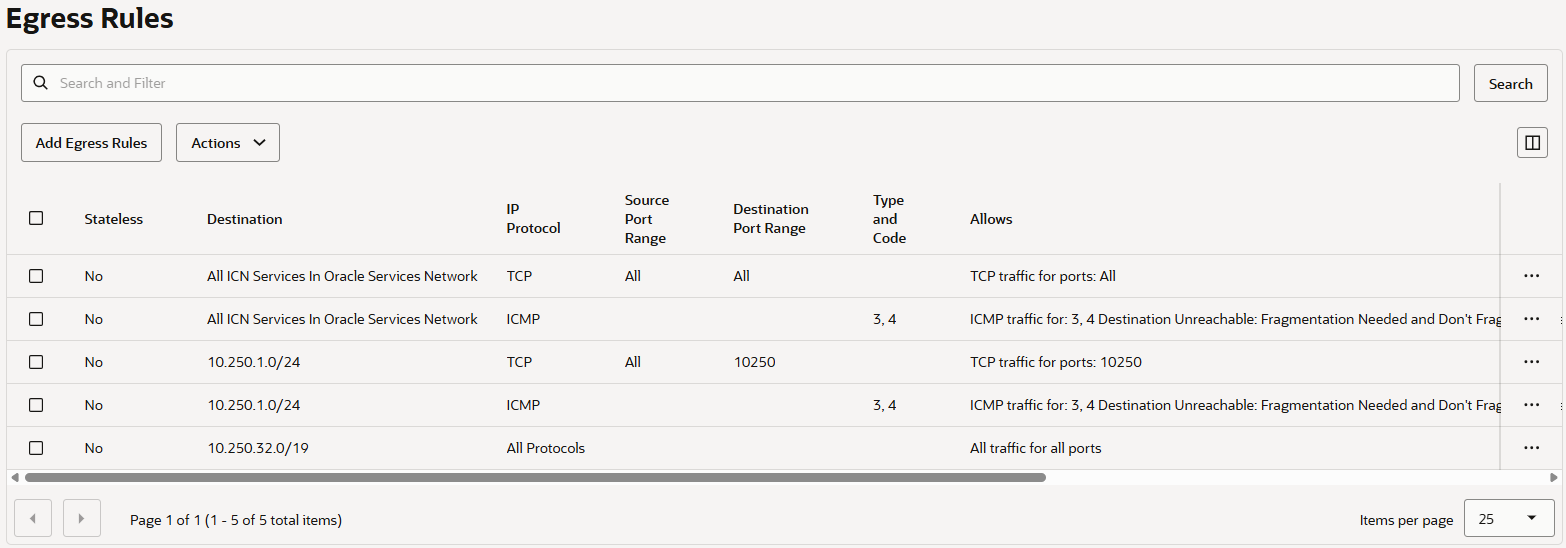
2.4.2. WorkerNode Subnet용 Security List 생성
Ingress
State Source Protocol/Dest. Port Description Stateful 10.250.0.0/29 TCP/10250 Allow Kubernetes API endpoint to communicate with worker nodes Stateful 0.0.0.0/0 ICMP 3,4 Path Discovery Stateful 10.250.3.0/24 TCP/22 Allow inbound SSH traffic to managed nodes Stateful 10.250.2.0/24 ALL/30000-32767 Load balancer to worker nodes node ports Stateful 10.250.2.0/24 ALL/10256 Allow load balancer to communicate with kube-proxy on worker nodes Egress
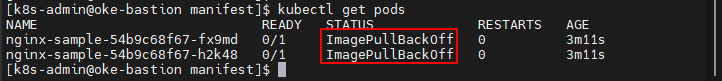
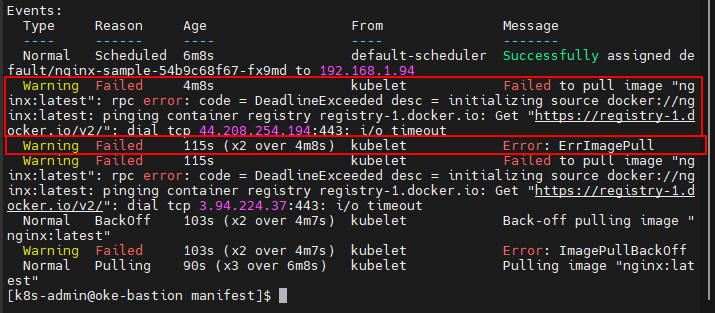
State Source Protocol/Dest. Port Description Stateful 10.250.32.0/19 ALL/ALL Allow worker nodes to access pods Stateful 0.0.0.0/0 ICMP 3,4 Path Discovery Stateful All ICN Services In Oracle Services Network TCP/ALL Allow worker nodes to communicate with OKE Stateful 10.250.0.0/29 ALL/6443 Kubernetes worker to Kubernetes API endpoint communication Stateful 10.250.0.0/29 ALL/12250 Kubernetes worker to Kubernetes API endpoint communication Stateful 0.0.0.0/0 TCP/443 (Custom) Accessing an external Public Image registry for kubelet
(optional) Accessing an external Public Image registry for kubelet
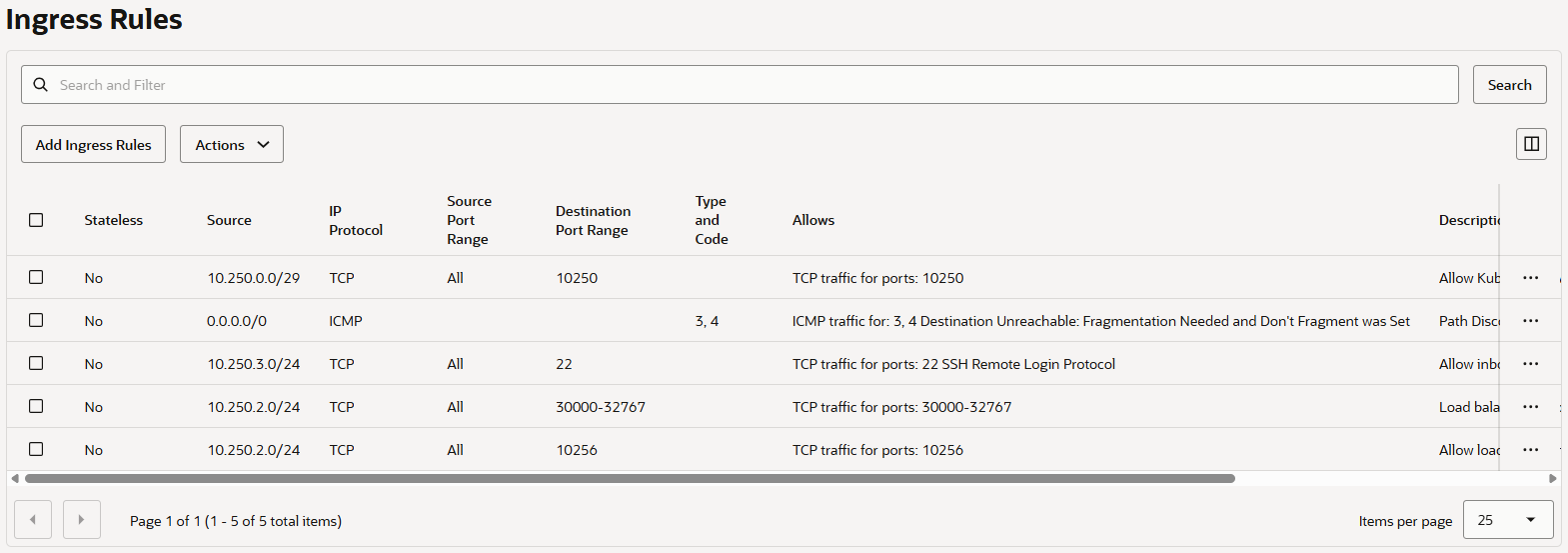
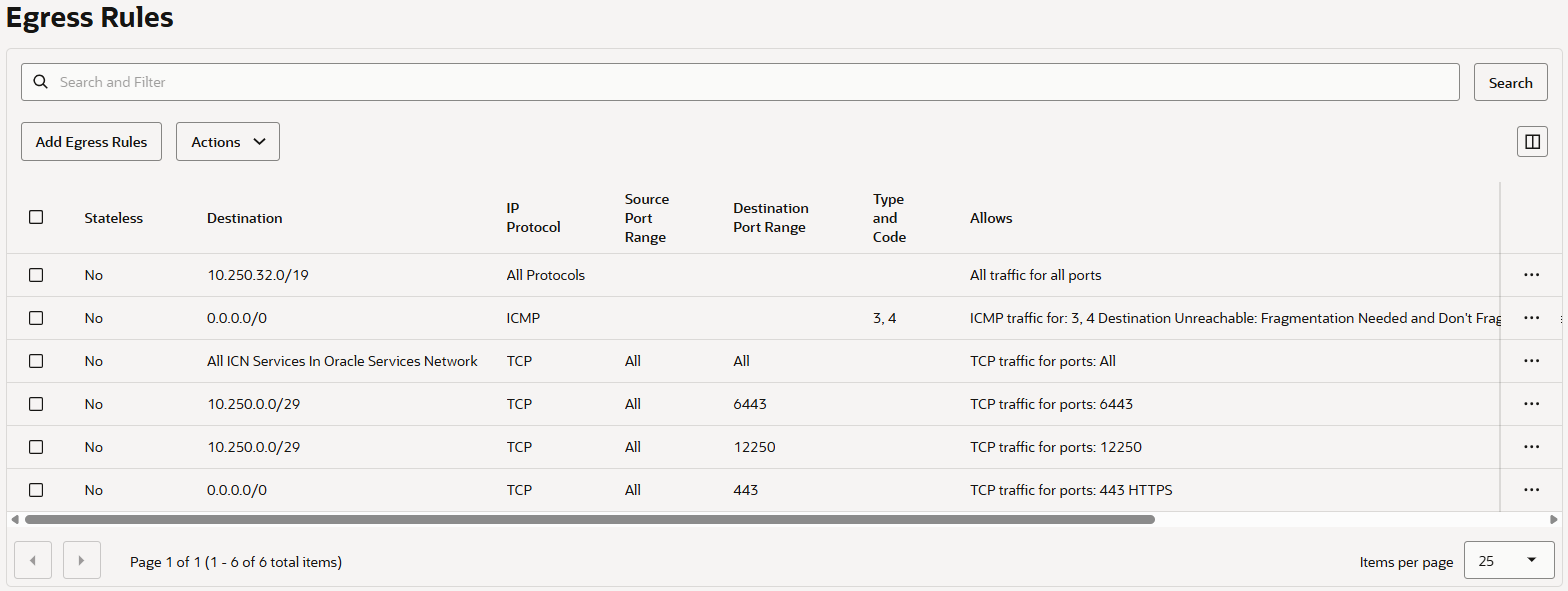
2.4.3. Pod Subnet용 Security List 생성
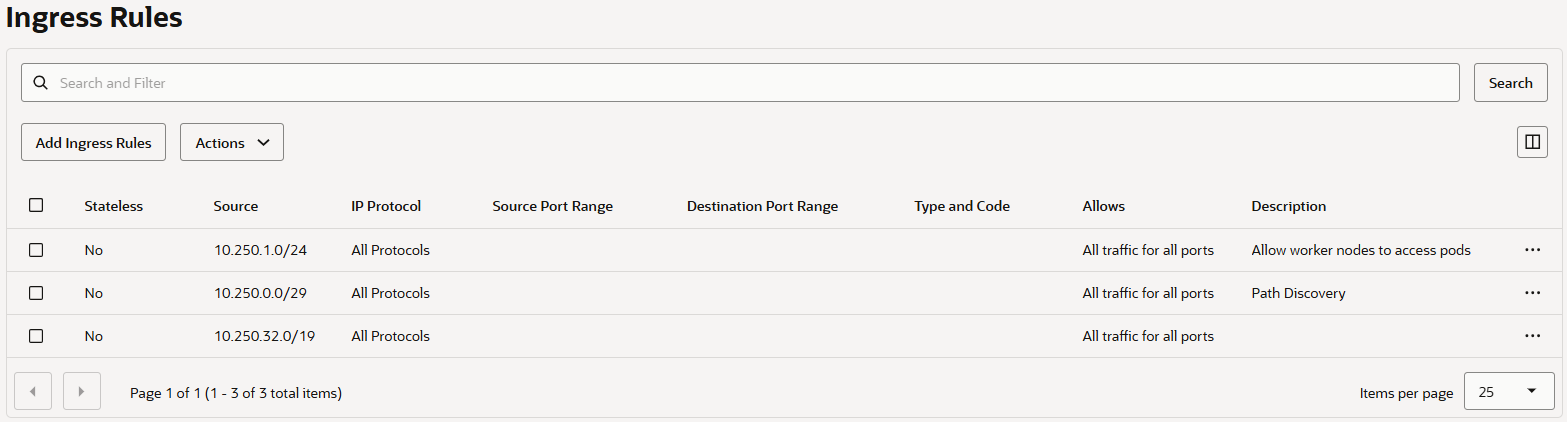
Ingress
State Source Protocol/Dest. Port Description Stateful 10.250.1.0/24 ALL/ALL Allow worker nodes to access pods Stateful 10.250.0.0/29 ALL/ALL Path Discovery Stateful 10.250.32.0/19 ALL/ALL Allow pods to communicate with other pods Egress
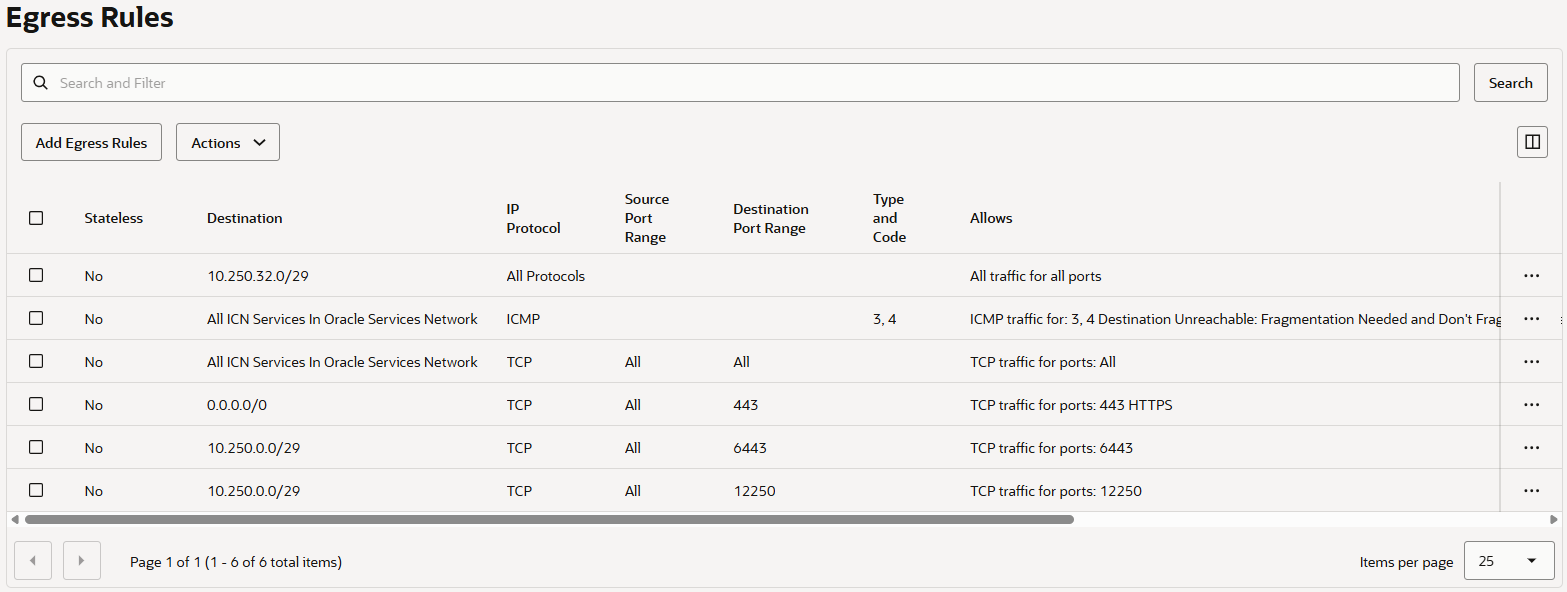
State Source Protocol/Dest. Port Description Stateful 10.250.32.0/29 ALL/ALL Allow pods to communicate with other pods Stateful All ICN Services In Oracle Services Network ICMP 3,4 Path Discovery Stateful All ICN Services In Oracle Services Network TCP/ALL Allow pods to communicate with OCI services Stateful 0.0.0.0/0 TCP/443 (optional) Allow pods to communicate with internet Stateful 10.250.0.0/29 ALL/6443 Pod to Kubernetes API endpoint communication (when using VCN-native pod networking) Stateful 10.250.0.0/29 ALL/12250 Pod to Kubernetes API endpoint communication (when using VCN-native pod networking)
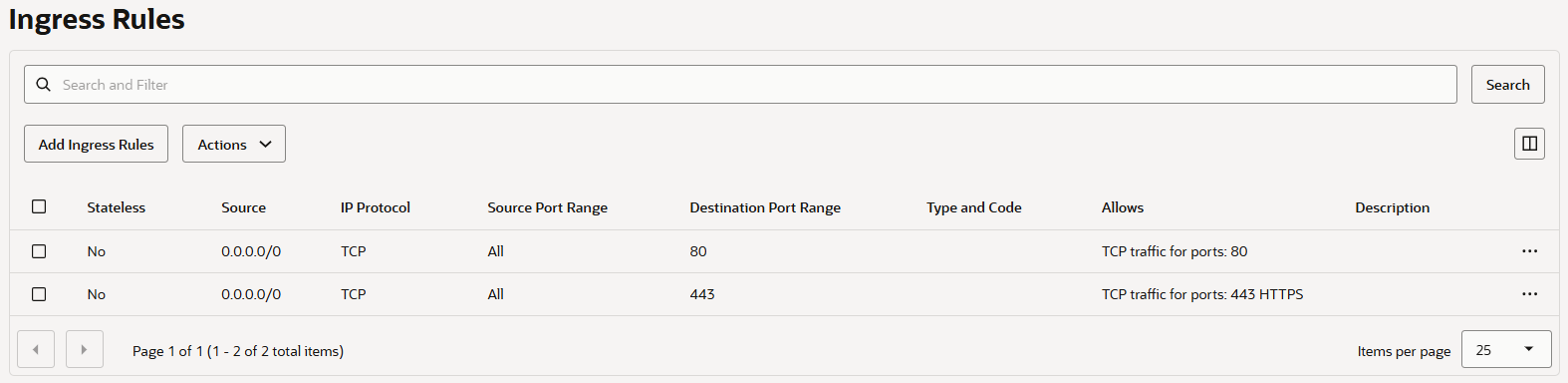
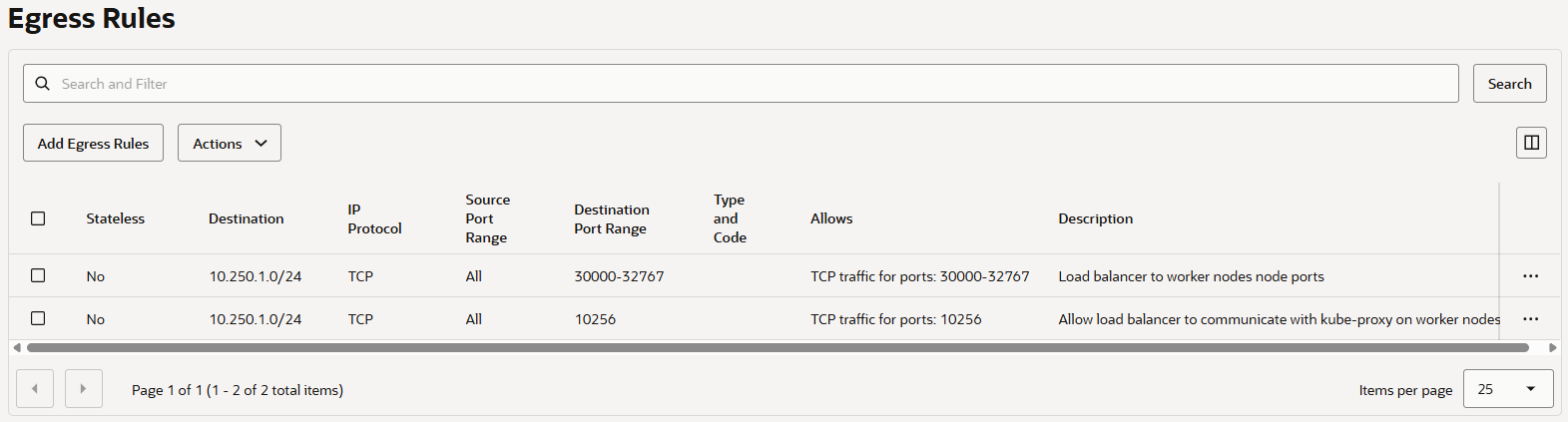
2.4.4. LB Subnet용 Security List 생성
Ingress
State Source Protocol/Dest. Port Description Stateful 0.0.0.0/0 TCP/80 Stateful 0.0.0.0/0 TCP/443 Egress
State Source Protocol/Dest. Port Description Stateful 10.250.1.0/24 ALL/30000-32767 Load balancer to worker nodes node ports Stateful 10.250.1.0/24 ALL/10256 Allow load balancer to communicate with kube-proxy on worker nodes
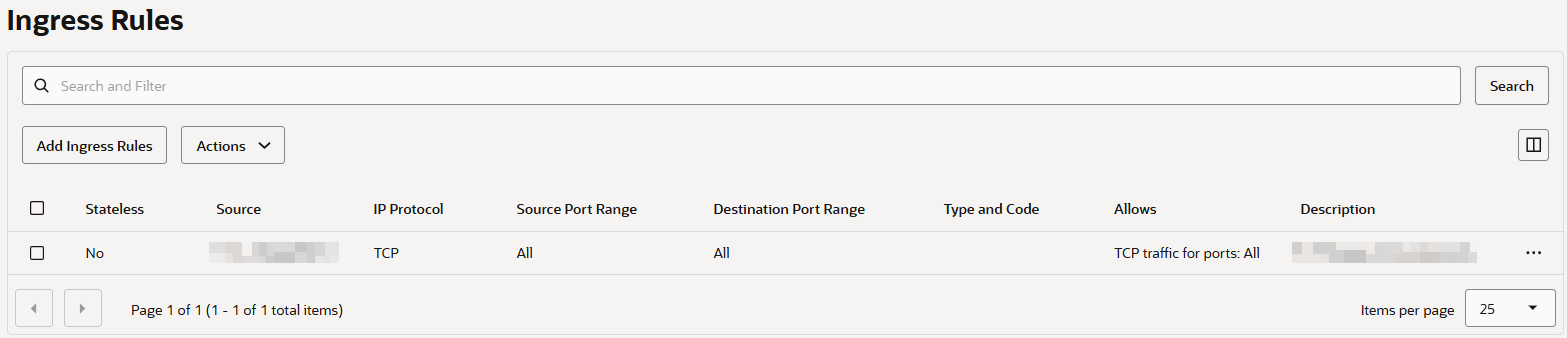
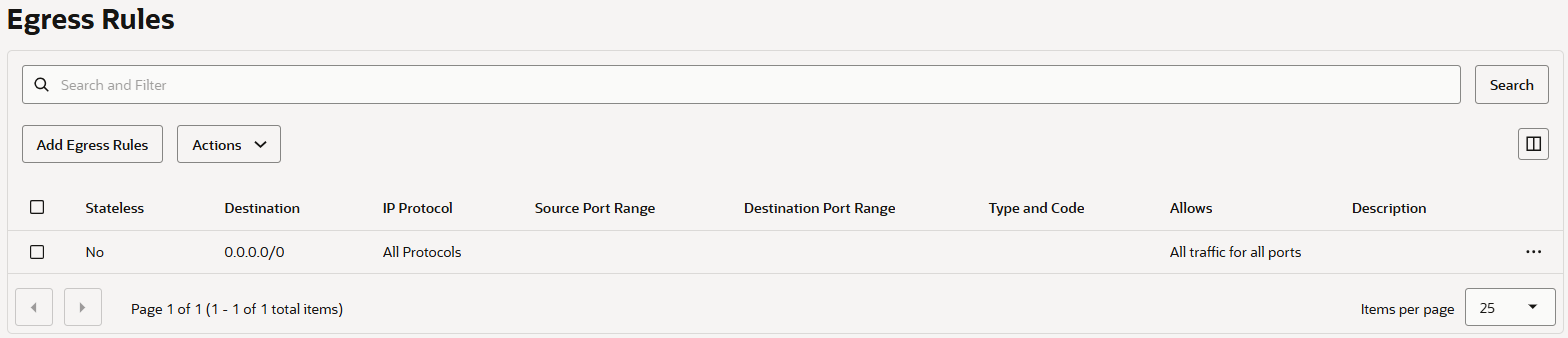
2.4.5. Bastion Subnet용 Security List 생성
Ingress
State Source Protocol/Dest. Port Description Stateful <Bastion 접속이 필요한 Public IP> TCP/22 <Description> Egress
State Source Protocol/Dest. Port Description Stateful 0.0.0.0/0 ALL/ALL
2.5. Subnet 생성
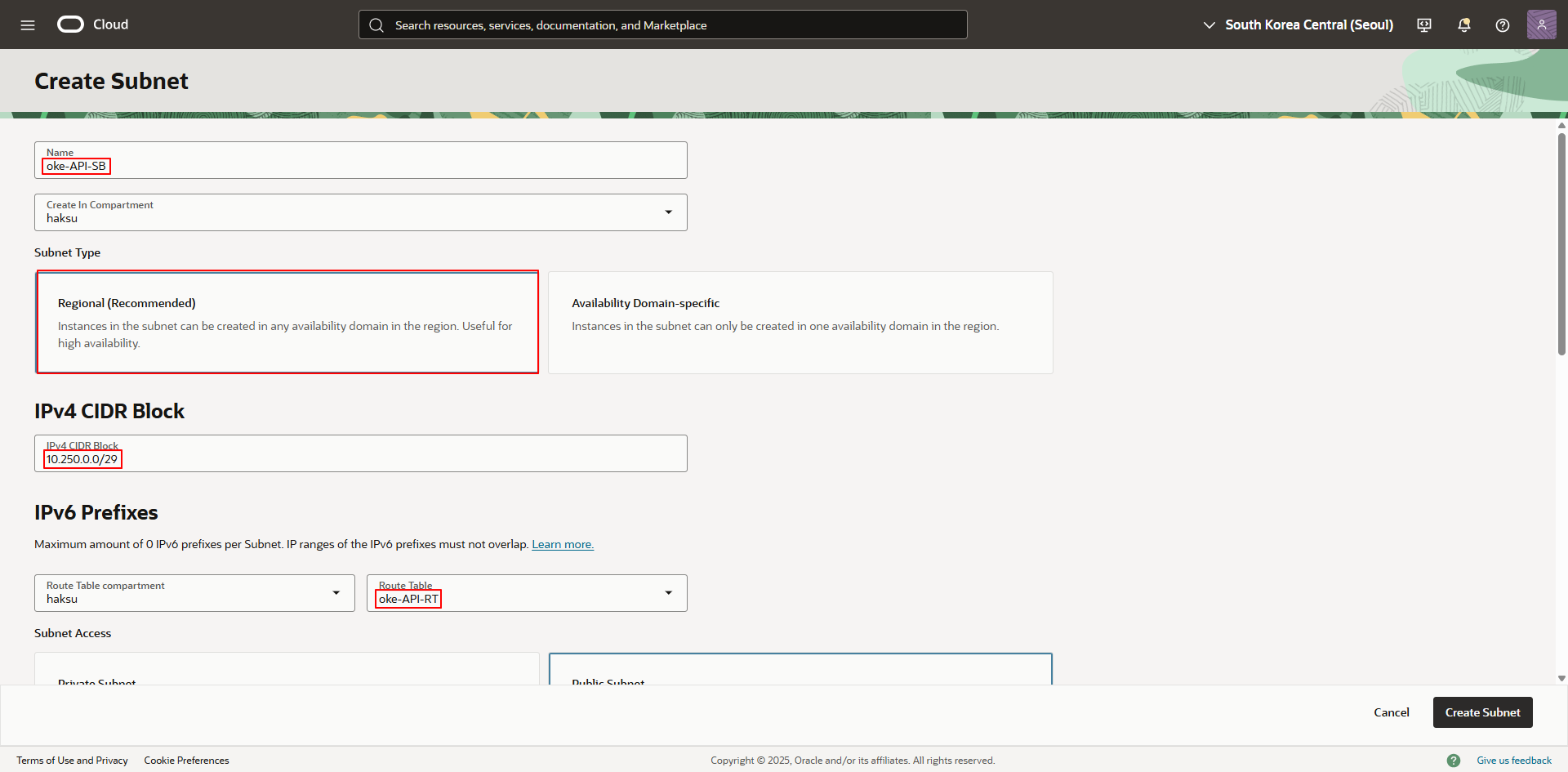
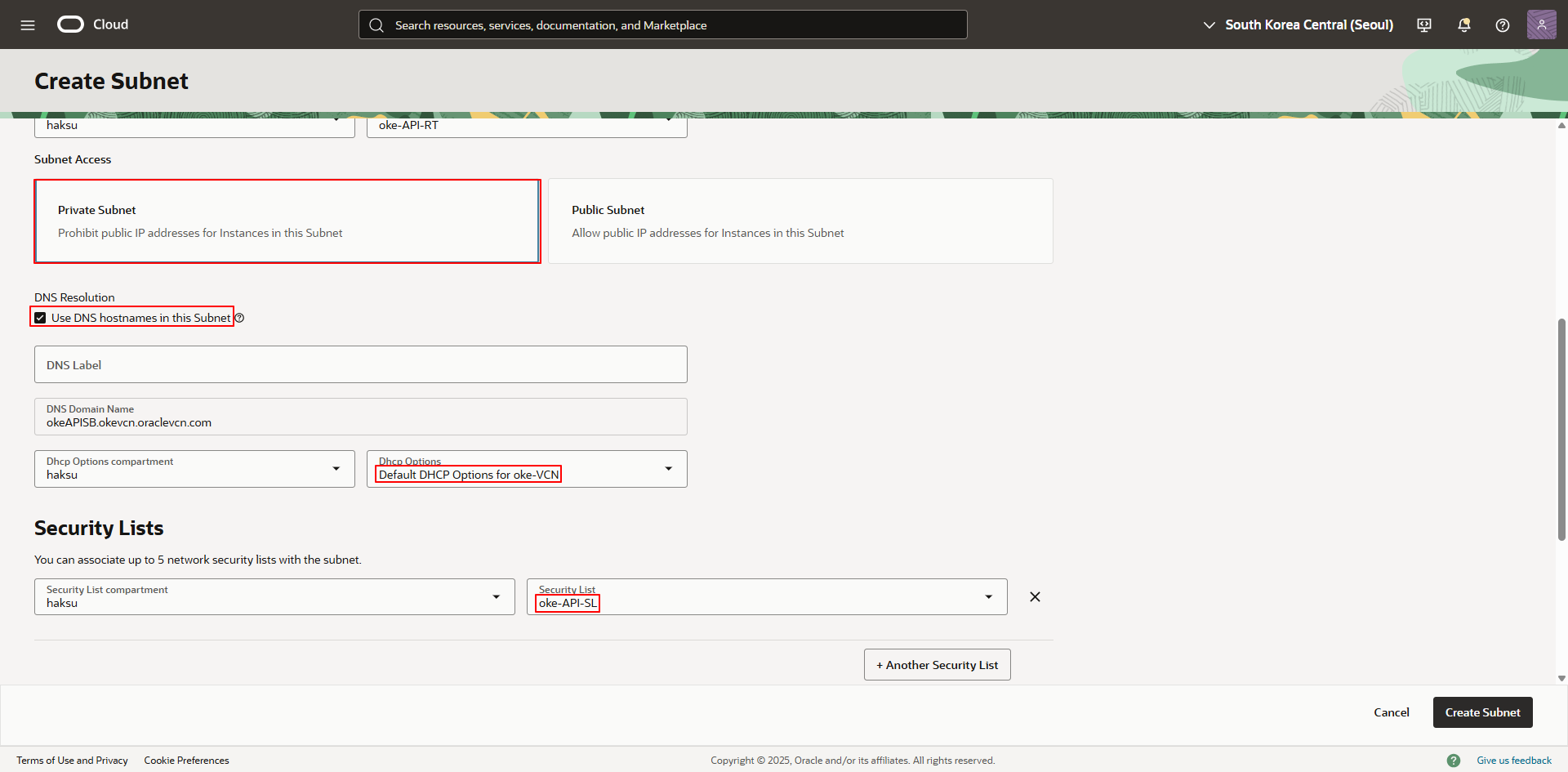
2.5.1. API Endpoint Subnet 생성
- Name : <적절한 이름 입력>
- Type : Regional
- CIDR Block : 10.250.0.0/29
- Route table : <API Endpoint Subnet용 Route table 선택>
- Subnet access : Private
- DNS Resolution : Selected
- DHCP Options : Default
- Security List : <API Endpoint Subnet용 Security list 선택>
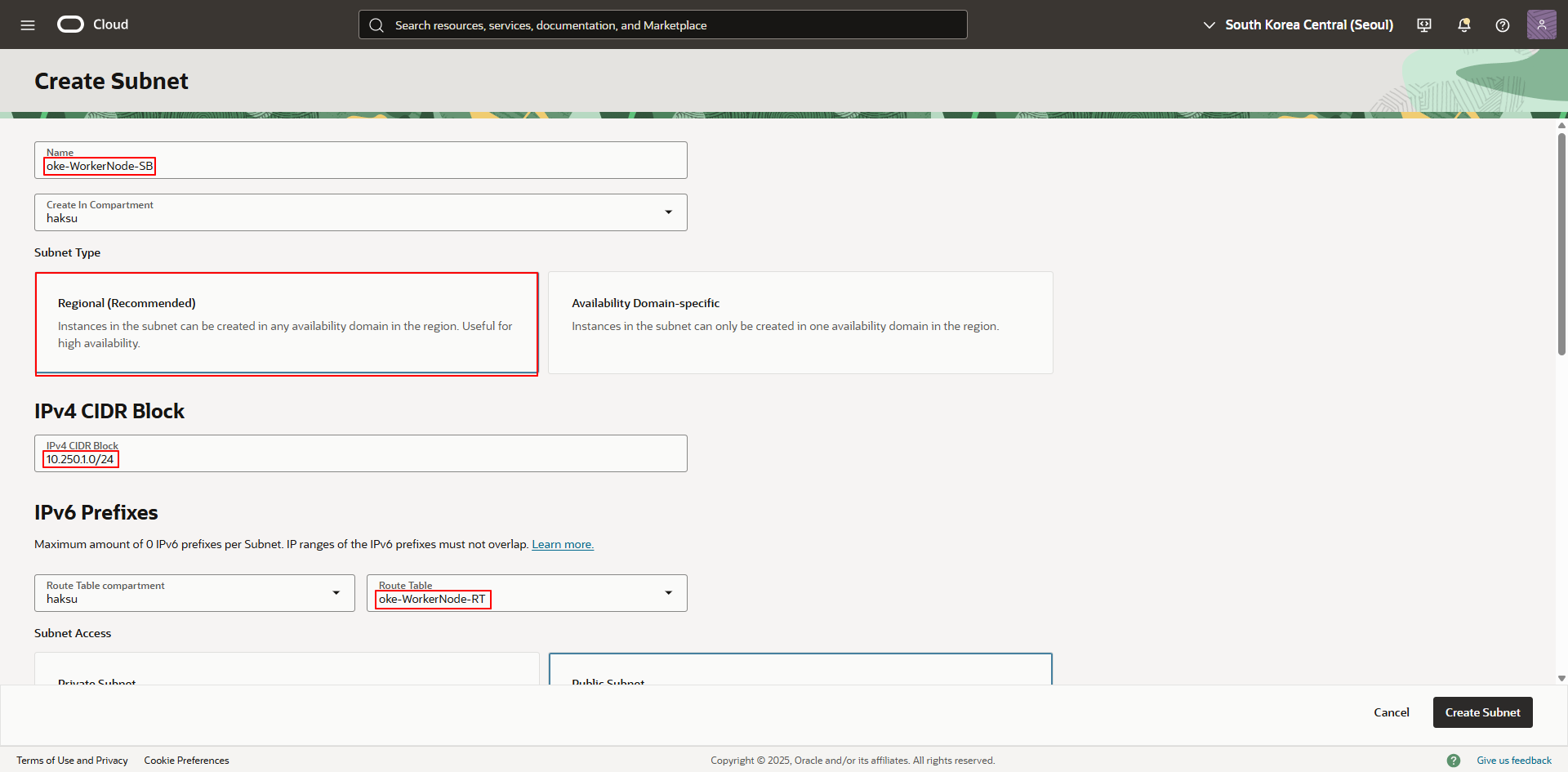
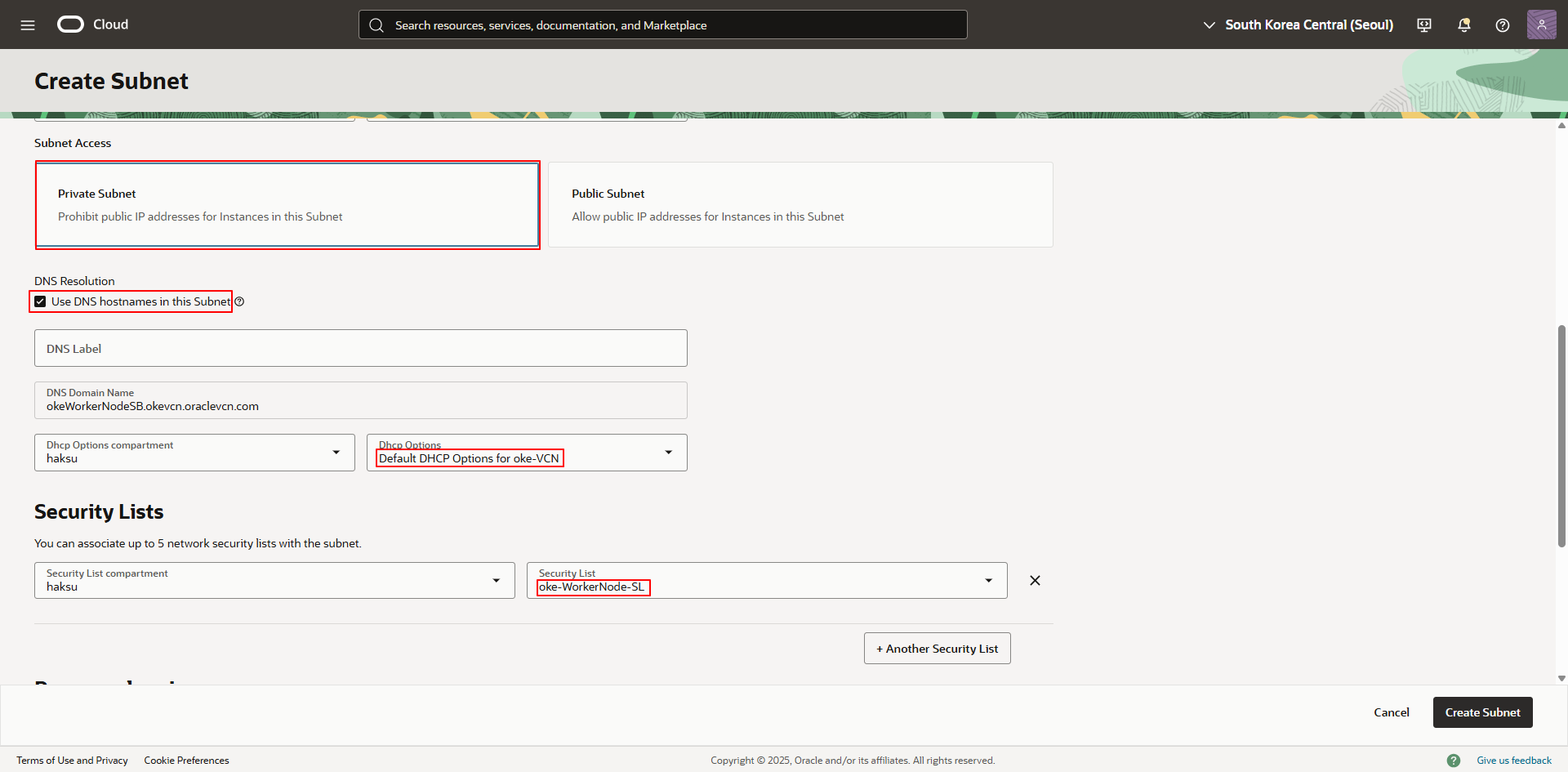
2.5.2. WorkerNode Subnet 생성
- Name : <적절한 이름 입력>
- Type : Regional
- CIDR Block : 10.250.1.0/24
- Route table : <WorkerNode Subnet용 Route table 선택>
- Subnet access : Private
- DNS Resolution : 체크
- DHCP Options : Default
- Security List : <WorkerNode Subnet용 Security list 선택>
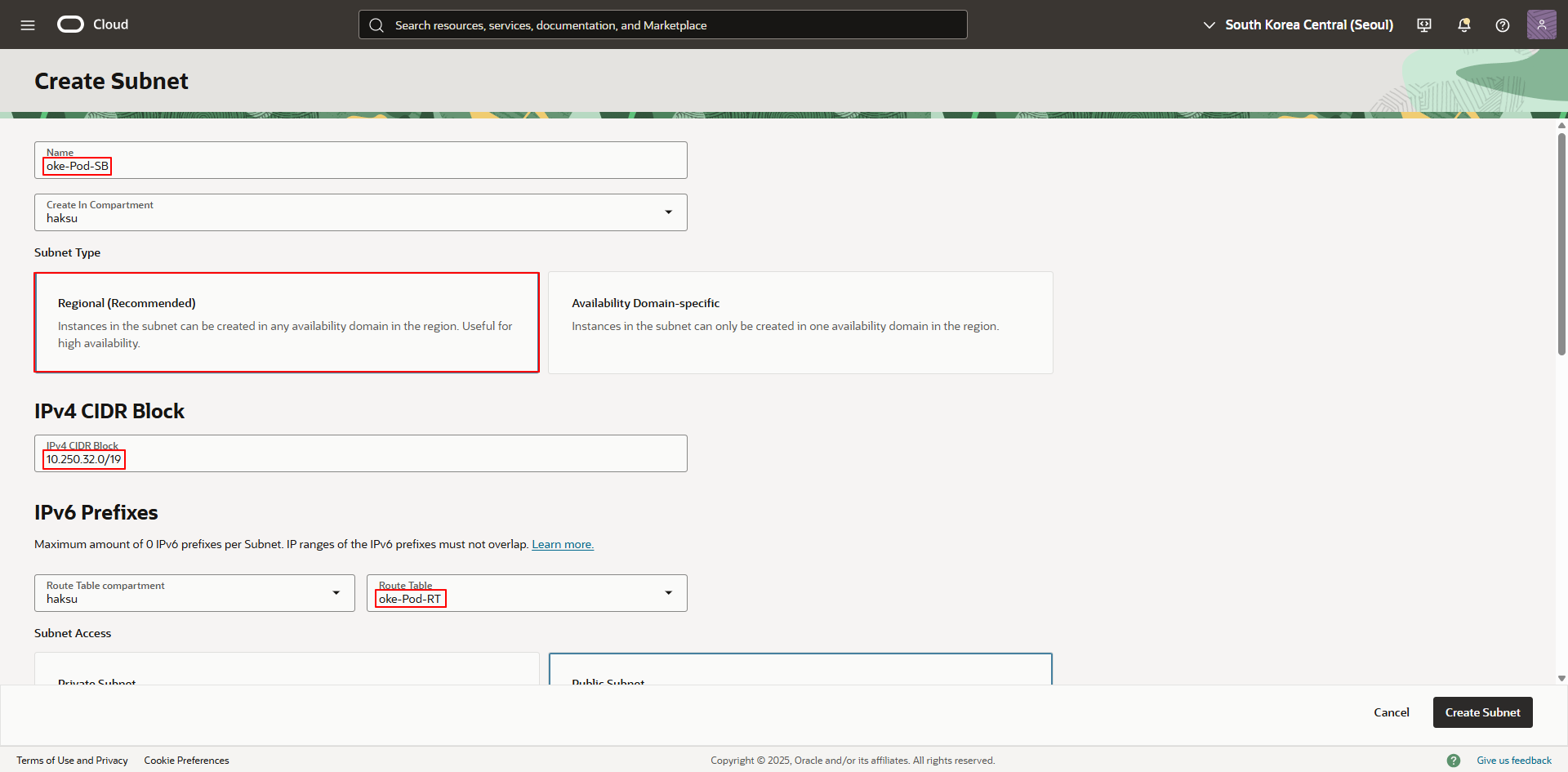
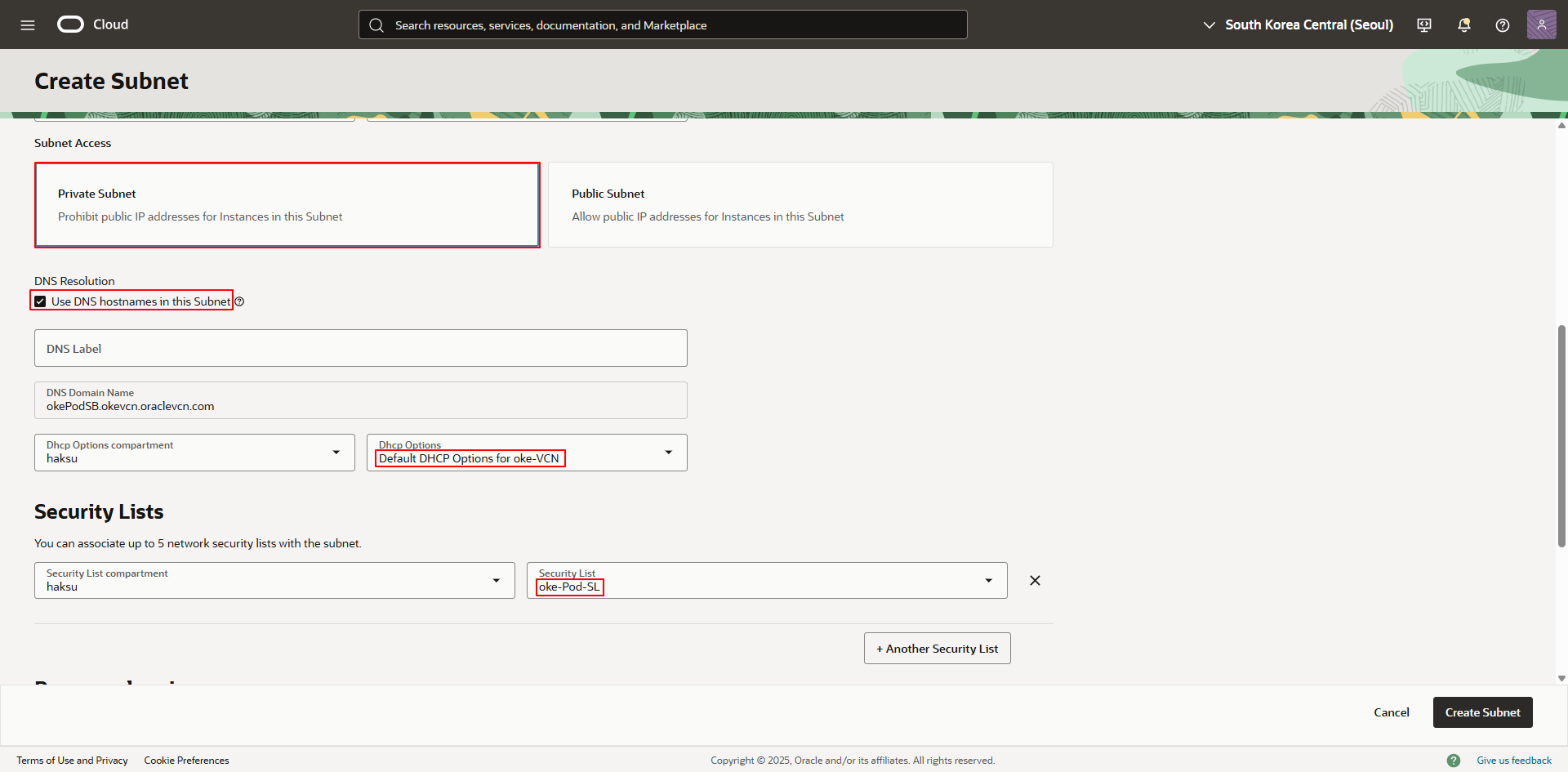
2.5.3. Pod Subnet 생성
- Name : <적절한 이름 입력>
- Type : Regional
- CIDR Block : 10.250.32.0/19
- Route table : <Pod Subnet용 Route table 선택>
- Subnet access : Private
- DNS Resolution : 체크
- DHCP Options : Default
- Security List : <Pod Subnet용 Security list 선택>
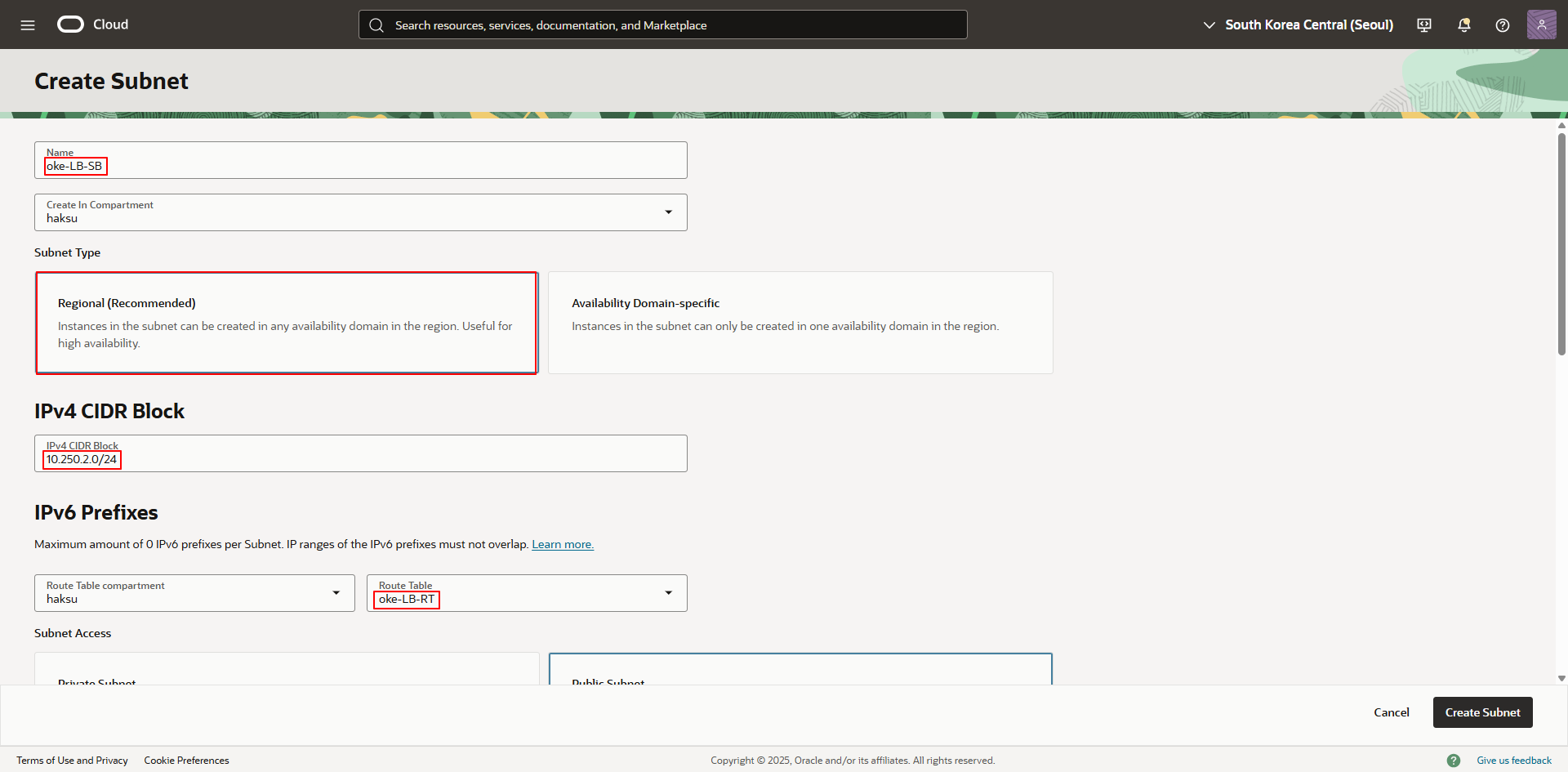
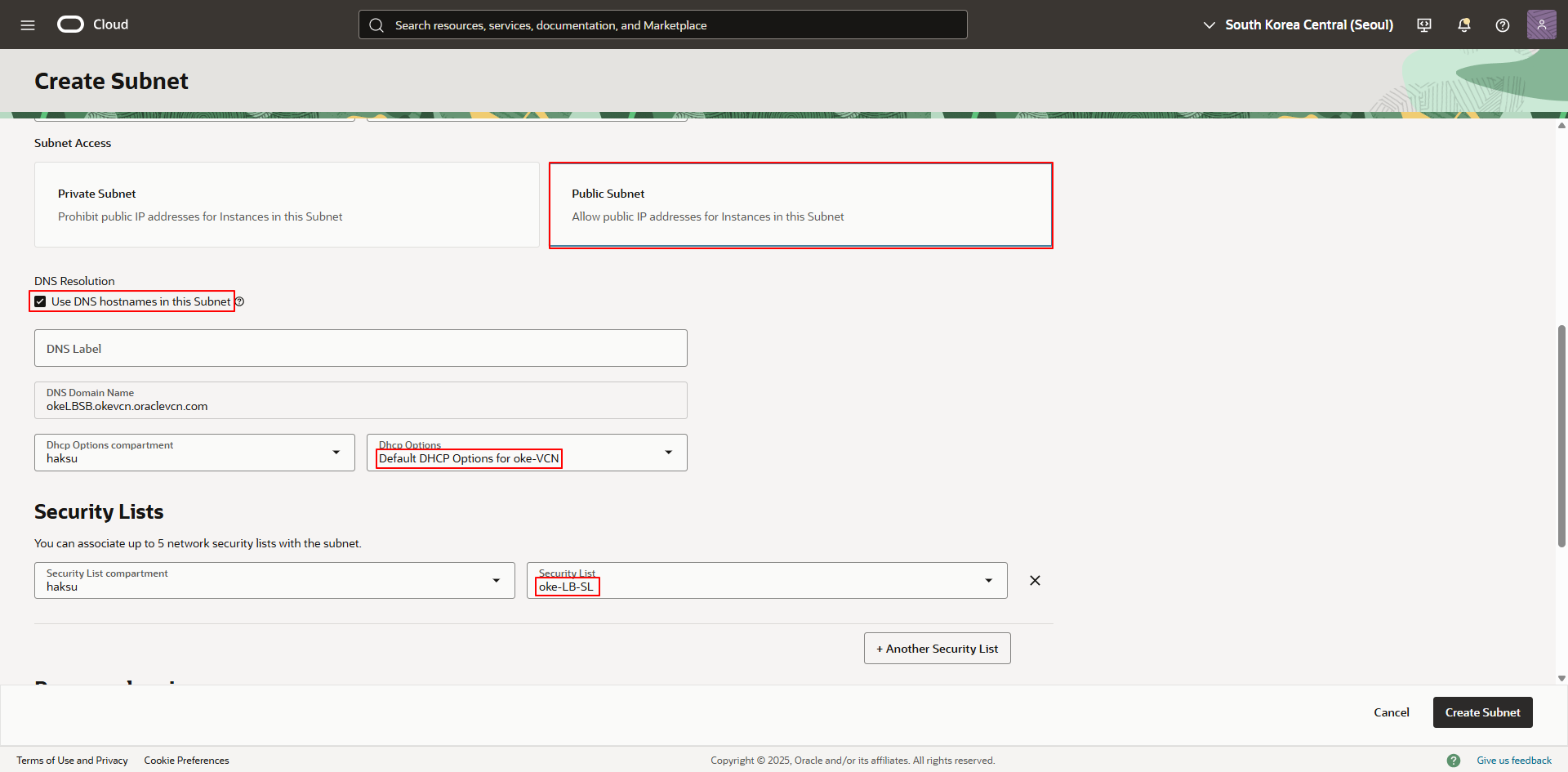
2.5.4. LB Subnet 생성
- Name : <적절한 이름 입력>
- Type : Regional
- CIDR Block : 10.250.2.0/24
- Route table : <LB Subnet용 Route table 선택>
- Subnet access : Private
- DNS Resolution : 체크
- DHCP Options : Default
- Security List : <LB Subnet용 Security list 선택>
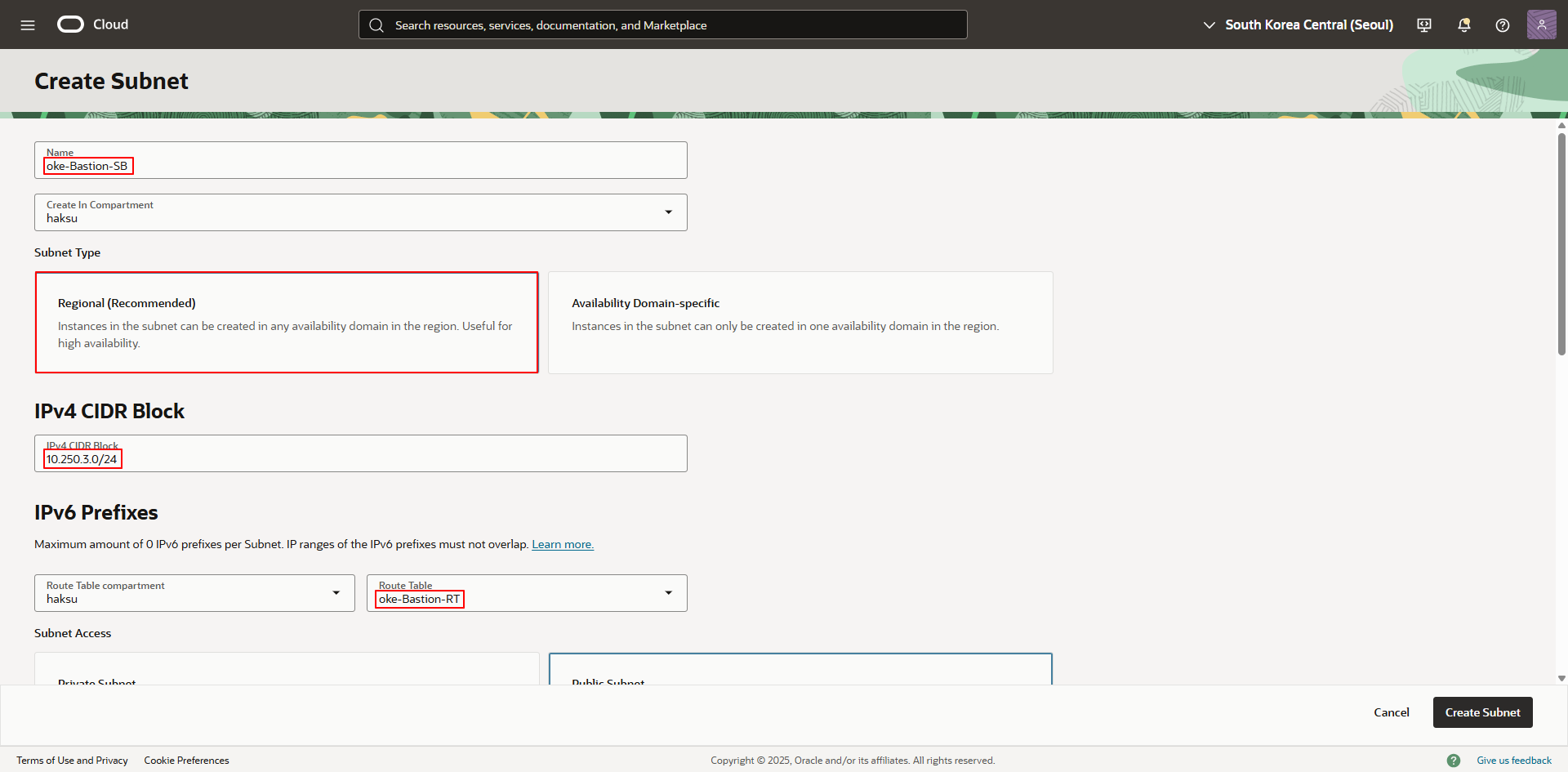
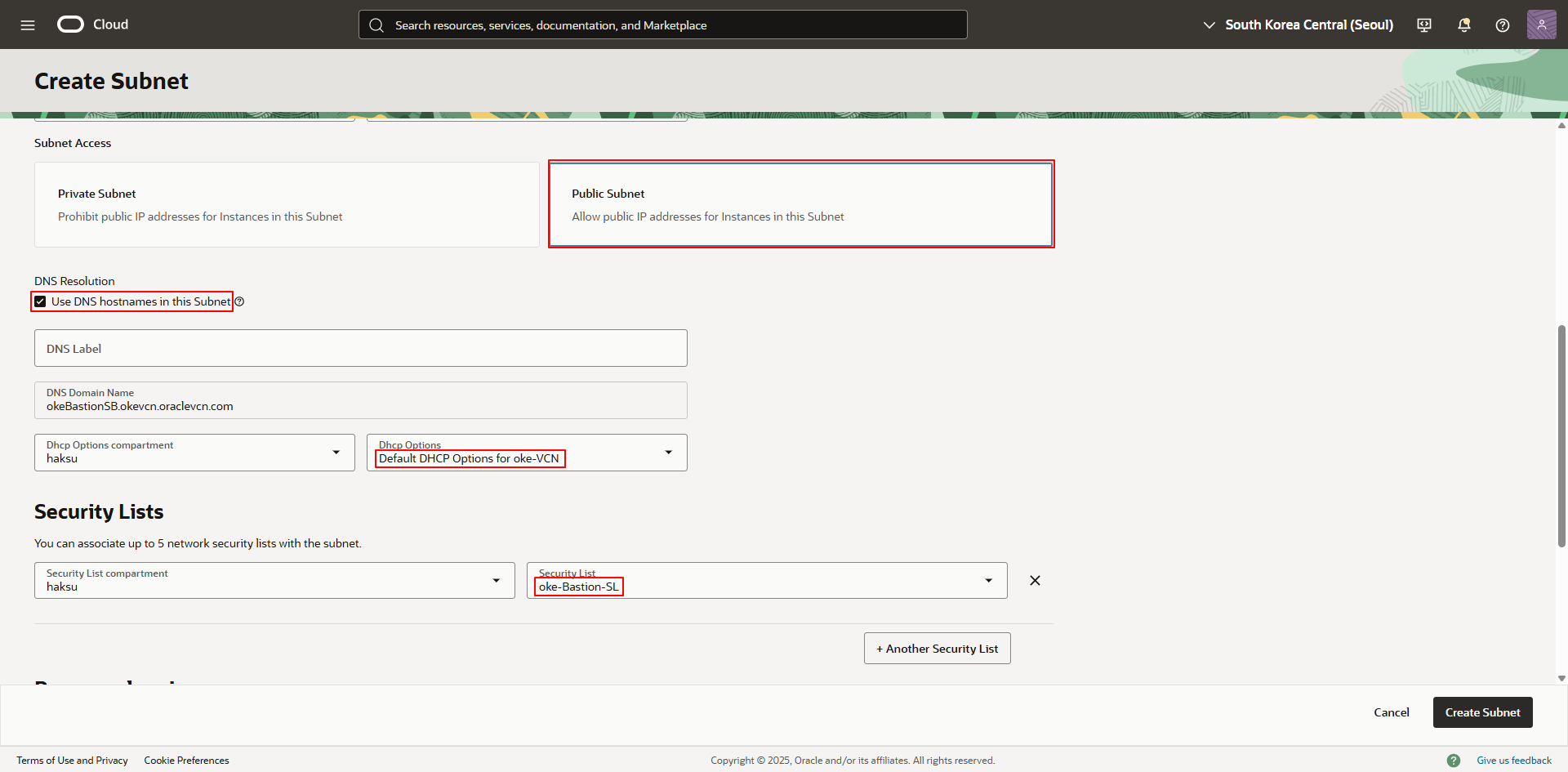
2.5.5. Bastion Subnet 생성
- Name : <적절한 이름 입력>
- Type : Regional
- CIDR Block : 10.250.3.0/24
- Route table : <Bastion Subnet용 Route table 선택>
- Subnet access : Public
- DNS Resolution : 체크
- DHCP Options : Default
- Security List : <Bastion Subnet용 Security list 선택>
This post is licensed under CC BY 4.0 by the author.